Greenfield backs Dapper Labs to further develop scalable Layer 1 Blockchain Flow
by Greenfield, Aug. 06
We are excited to share today that we have joined Dapper Lab’s recent $11.3m funding round alongside USV, a16z, AppWorks, Samsung NEXT, Coinbase Ventures, Venrock, Accomplice and others.
The team is building a scalable layer 1 blockchain, initially focused on gaming and entertainment. Their unique go-to-market strategy involves content partnerships with large consumer brands such as the NBA (several NBA players including Aaron Gordon and Spencer Dinwiddle invested in this round) or UFC in order to break into the mainstream market with blockchain collectible games (both in-house game development and over time more and more 3rd party developers). Thus, they have an amazing opportunity to achieve industry standard status by showcasing compelling branded mainstream killer dapps. Starting out with gaming Flow will be perfectly positioned to expand into further avenues, as developers see its benefits in practice.
Flow’s blockchain beta mainnet has been launched recently, benefitting from a vibrant community: 1000+ developers, 400+ students in the Open World Builders program, ~100 projects in the pipeline from known teams including venture-funded startups as well as Fortune 500 companies.
Opportunity
Blockchains will reshape how we use and interact with digital worlds, but it is not scalable & usable enough yet. While the global online gaming market is forecasted to reach $286bn by 2027, gaming is not the only opportunity for Dapper Labs and Flow. The exciting part about the project is that they are aiming at the general purpose blockchain market, with a unique gaming & entertainment brand focused go-to-market strategy.
Gaming on the blockchain — digital provable scarcity for game items
When speaking about blockchain gaming, it is important to first highlight, that gaming experiences, which often tend to be computationally intensive and involving sophisticated graphics will not be executed on-chain. However, important aspects about a game such as in-game assets like characters and items are represented on a decentralized blockchain through non-fungible tokens and are thus truly owned by users, as the blockchain operates independently of any gaming company that originally initiated and produced the content. What is more, core game logic, that define the rules of how a game is to be played could be represented in smart contracts (CryptoKitties and Cheeze Wizards are examples of this).
This is crucial, when thinking about how much time and money gamers often invest in playing, building their character (leveling up etc.) and collecting items. In many instances these types of gamers spend the majority of their time in a gaming environment (which demonstrates the importance of games to many, leading to a high willingness to spend). In fact, the following quote from Ethereum founder Vitalik Buterin illustrates the point quite well: “I happily played World of Warcraft during 2007–2010, but one day Blizzard removed the damage component from my beloved warlock’s Siphon Life spell. I cried myself to sleep, and on that day I realized what horrors centralized services can bring.”
Also, giving players governance power over game dynamics can be a powerful avenue — creating community owned virtual worlds.
Additionally, gamers are already familiar with the use of virtual in-game currencies and are thus a natural audience for blockchain based tokens (e.g. World of Warcraft gold — there is even an industry of gold farmers, players that play to earn gold in order to sell it on — which could be extended into crypto).
Increased perceived value for gamers due to truly owned assets & tradability
Previously, there have been grey-markets for in-game items in cases where they are transferable. However, there is no true sense of ownership, as the issuing company dictates the terms under which the digital assets are to be used. When users truly own their digital assets on a decentralized, independent blockchain, they are willing to spend considerably more due to the higher degree of certainty of their possession with NBA Top Shot generating already $1.2m. in pre-sale revenue from the first 500 players. What is more, there is likely to be a more liquid market for such assets and exchanges for non-fungible tokens (e.g opensea — 90k ETH total trading volume so far). Gamers can play to earn in a more reliable and independent fashion than previously possible (see how to make a living in crypto gaming exemplified with collectible game Axie Infinity). Due to the greater certainty of ownership, users have shown a greater willingness to spend (see below: consistent average spend of >200$/player for CryptoKitties).
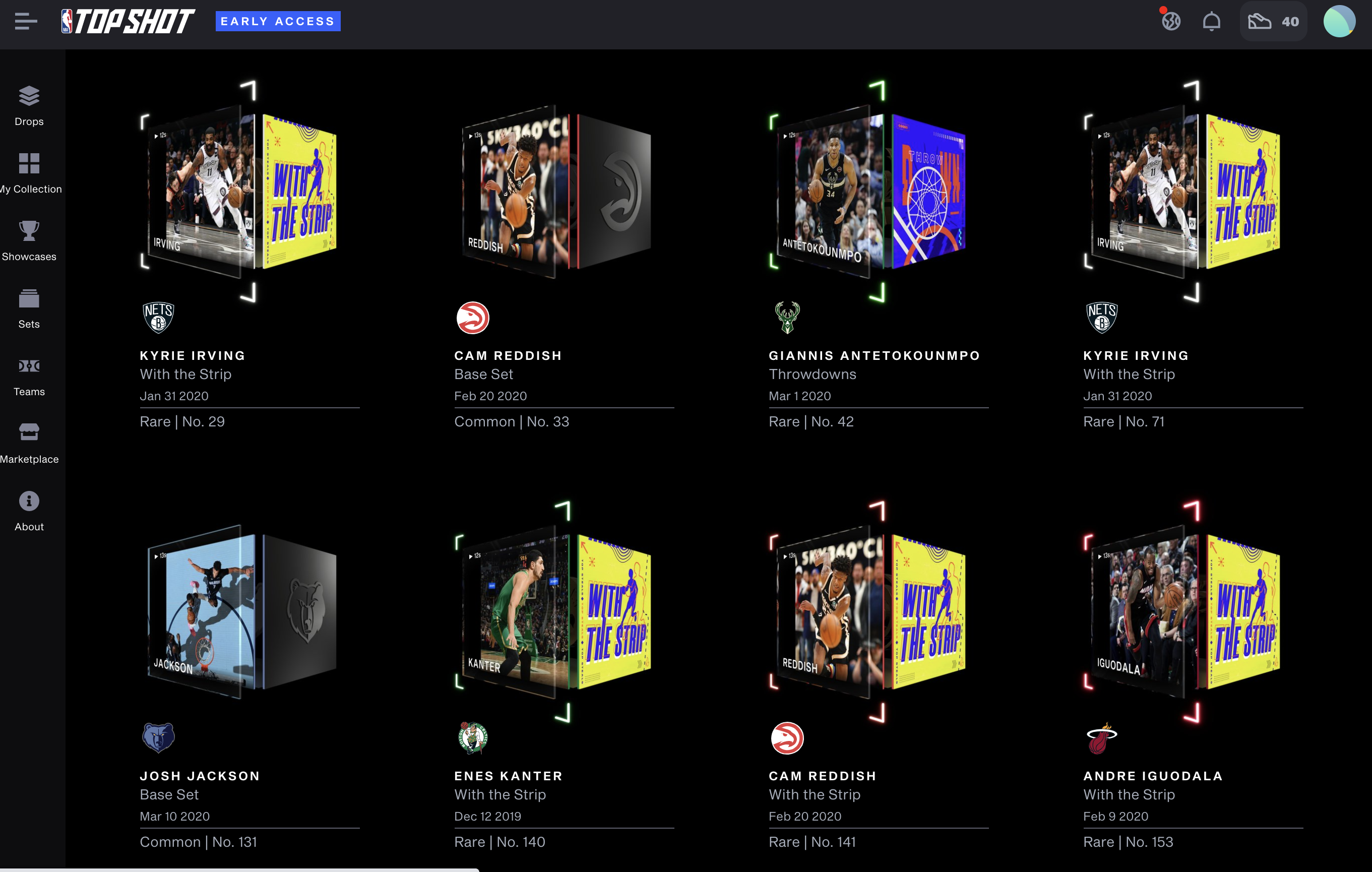
NBA Top Shot With The Strip Wave 1- 4 Pack Opening — cryptoed
In addition, decentralized finance is starting to show the power of composability, as assets originated in one protocol (e.g. MakerDAO stablecoin DAI) can be lent in the next (e.g. in Compound — a user receives a token that represents their interest bearing position), which can be further placed in a liquidity pool (e.g. Uniswap) to further enhance yield. NFT based in-game items and collectibles will enable similar behaviors, especially as they represent completely crypto-native assets, that do not depend on e.g. a custodian holding the property title of a tokenized real-estate asset as an interface. Early projects to enable collectible-collateralized lending are already experimented with (e.g. Rocket Loans).
Game interoperability & permissionless innovation
With standardized non-fungible tokens that represent in-game assets, anyone can build novel or altered games or add-ons that are compatible with the items. In the history of gaming, some of the most successful games have actually been community mods (e.g. Counter Strike emerged as a mod of Half Life). Porting over items from one game to another might not make sense in all instances, as game dynamics should be balanced for a good experience, but there might be community governance, that decides upon what kind of items are allowed in a certain game and which not, and many in-game assets might be only of aesthetic value. Such initiatives can however also be based on the originator companies such as with the cooperation between Dapper Labs and God’s Unchained to have certain kitties being used in both worlds.
Mainstream appeal of digital collectibles
The appeal of blockchains regarding for true digital player-ownership is not limited to hard-core gamers. Collecting special and scarce items has been an integral part of human behavior ever since.
As the digital realm gains importance in our lives, so will digital collectibles. Digitally native, reimagined forms of sports cards (see NBA topshot) and digital trading card games (see Gods Unchained) inspired by Magic the Gathering and others are just the beginning (fun fact: Mt.Gox, the infamous early Bitcoin exchange started out as “Magic the Gathering online exchange” in 2009).
Accessories in VR & AR
Even though, virtual/augmented reality has been discussed and worked on for decades now, and it is controversially discussed whether one or the other will be bigger, the technologies are getting ready for prime time. Standalone VR headset Oculus Quest with inside-out tracking (cord-less, external sensors free spatial tracking, without the need for a strong gaming PC) has been selling out last christmas and the popular game series Half Life for the first time launched a VR only title. In addition, Apple continues to push AR/VR, aiming at a launch of an entertainment/gaming & virtual meeting focused headset in 2021/22 and a lightweight pair of glasses for everyday mobile use after that. It has to be said though, that there has been a history of postponing such plans. On the other hand, mobile already is an AR platform today, with Pokémon Go as a great example of collectible gaming ($894M user spending in 2019). In all such virtual worlds (in and outside of gaming) there will be the potential for scarce and unique digital items or users to enjoy, pride themselves with, collect and maybe sell them for a profit later at some point (e.g. digital fashion). As people invest more time and money in their virtual outfits and accessories, they will become vary of single companies providing them access to their digital possessions. They will demand an independent and internet native property register for their belongings, that can outlive the originating company and even themselves for generations to come.
It begins with CryptoKitties
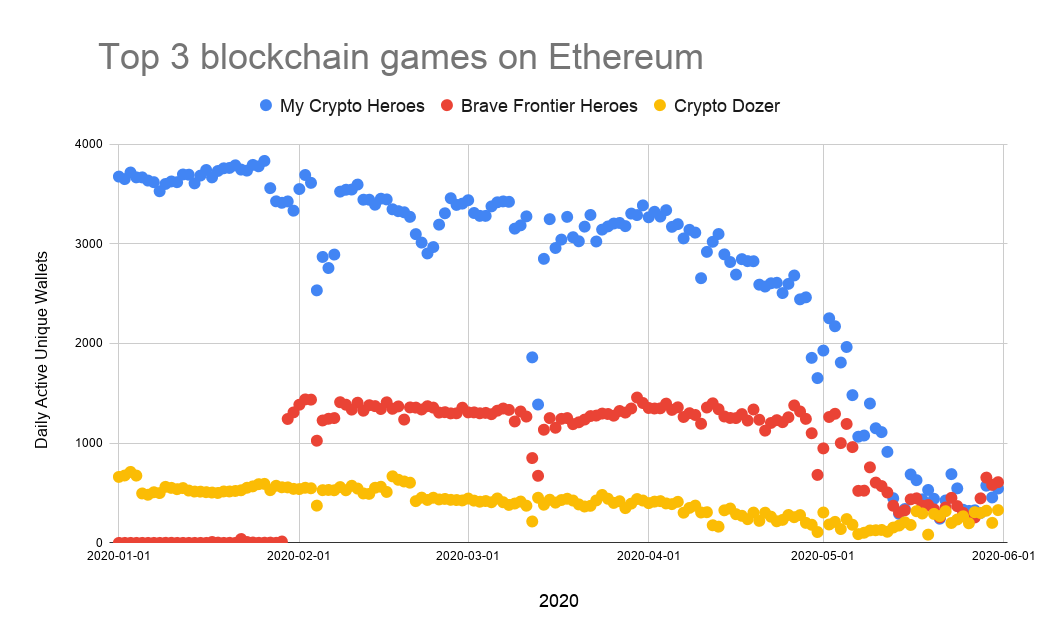
Also more recently, during May 2020, all games running on the Ethereum blockchain saw daily activities collapse, due to high transaction costs, without reaching significant scale yet. An expected further boom in decentralized finance activity will likely further worsen the situation for gaming, as high-value finance users are willing to spend considerably more on transaction fees than lower value gamers.
Dapper Labs is building Flow
The Dapper Labs team has shown an extensive track record in venture building, mobile as well as blockchain gaming, having experienced the pain points of building on Ethereum first-hand (inventing the ERC-721 standard for non-fungible-tokens on Ethereum with their blockchain game CryptoKitties and subsequently Cheeze Wizards).
As a result, they are perfectly positioned to build their differentiated blockchain with a novel scaling solution (that provides unproblematic composability of dapps and contracts) and a top-notch developer as well as user experience.
Cadence, their novel easy-to-learn programming language specifically designed for dapps & digital assets, will compile to Libra’s Move virtual machine for interoperability purposes.
Scalability
Flow proof-of-stake consensus (based on a variant of hot-stuff) scales by splitting tasks into chunks, that are collected, processed and included into blocks by different classes of nodes, in a similar way as modern multi-core processors handle tasks. Powerful execution nodes process the full state, which enables atomic transactions within 1 block for any application on the platform.
Specifically, the selection and ordering of transactions are performed independently from their execution. This approach achieves scaling via separation of concerns (better utilization of network resources). Thus, established programming paradigms can be used for smart contracts (which generally assume transactional atomicity) to persist without introducing additional complexity. A major insight is that, one can separate the majority of computation and communication load from consensus without compromising security.
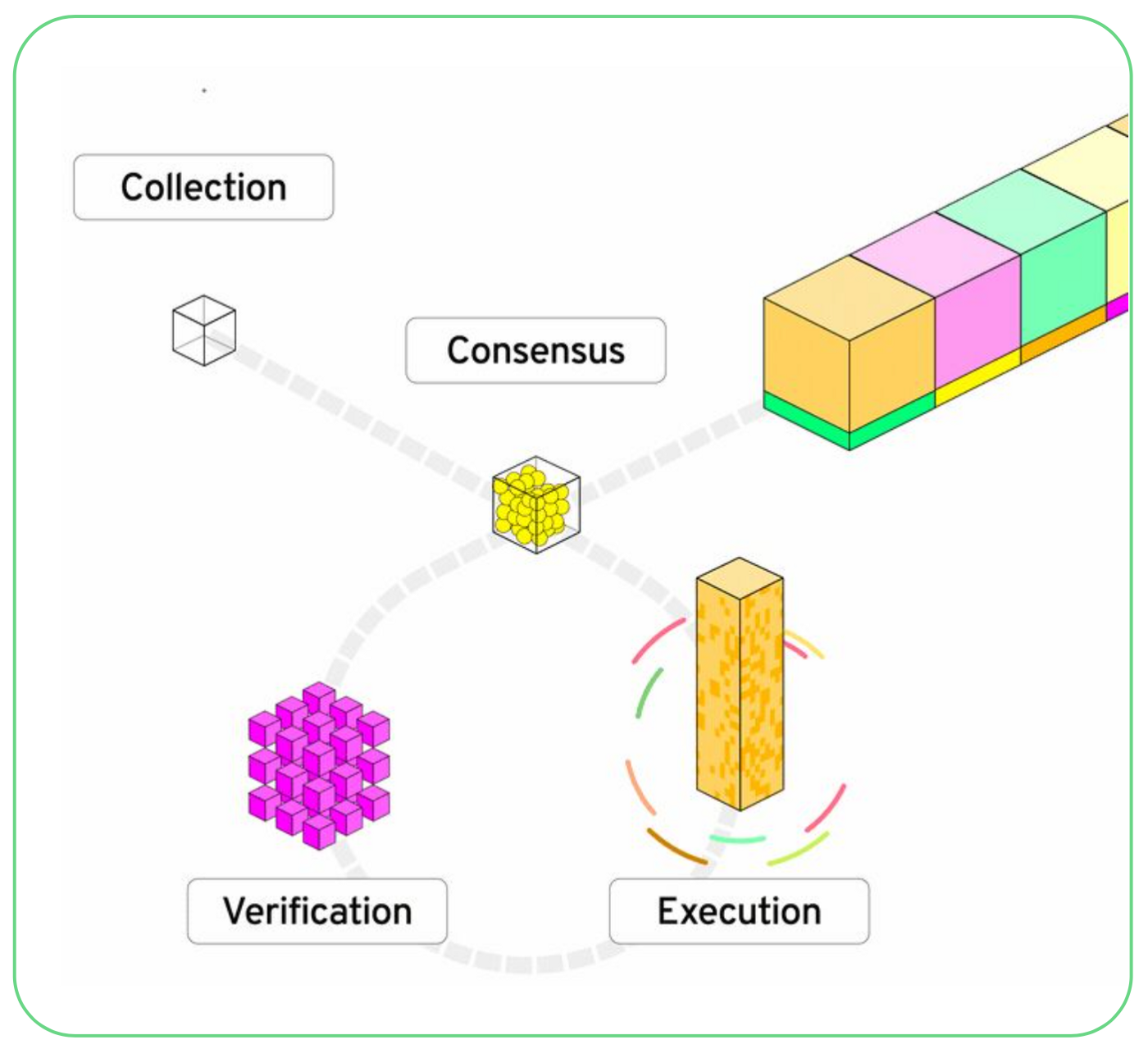
Collection nodes (medium number, high-speed internet connection required)
Collection nodes are divided by the protocol into cooperating clusters and are assembling transactions into collections. They are verifying that transactions are valid to then forward commitments to collections to consensus nodes (stake in fixed increments). Each node in a cluster receives equal work and is compensated in proportion to their stake.
Consensus nodes (large number for decentralization, low hardware requirements)
Consensus nodes form and propose blocks, as well as ensure the security of the network. Consensus nodes can stake in any increment without seeing a disproportionate increase in work, which could otherwise make participation prohibitive (consensus is assigned on a per-vote basis). This is important to allow a large number of decentralized nodes in order to prevent corruption and increase resilience.
Execution nodes (small number of powerful machines/data-centers for scalability)
Execution nodes are executing transactions and maintaining the execution state. Execution nodes must stake in fixed increments with relatively high minimum stake, which should make it expensive for these nodes to fall offline. They receive ordered and finalized chunks of transactions from consensus nodes, and then request the underlying data from collection nodes (which get slashed if they cannot do so). Execution nodes ensure scalability of the network (and will further scale with Moore’s law).
Verification nodes (large number for decentralization, low hardware requirements)
Verification nodes are checking chunks, a fixed unit of work and must stake in fixed increments to ensure they are not assigned more than they can effectively handle (no maximum number of participants in the verification process: anyone can stake to join). Verification can be parallelized and thus can scale over a large number of weaker nodes compared to execution. The concept of specialized proofs of confidential knowledge are used to solve the verifiers dilemma (that nodes could actually not do the work of verification and still get the reward; see tech paper 3 for details). Observed faulty executions are reported to the consensus nodes (with a cryptographic proof), which adjudicate the received challenges and slash malicious actors. While the architecture can significantly increase throughput, verification nodes still have to duplicate the computation fully.
As the security of a decentralized system is directly related to the number of independent participants working to secure the network, Flow supports large numbers of participants with diverse technical, as well as financial commitments, leading to a system with low barriers to participate, while being costly to subvert.
Go-to-market: mainstream brands to drive mainstream adoption
Dapper Labs has been fantastic at winning over household brand names, first and foremost the NBA to develop the Top Shot collectibles experience as well as a triple A mobile game (16% of US americans surveyed are avid fans, 31% casual fans + large international fanbase). NBA Top Shot, which captures the nostalgia of trading cards and the thrill of sneaker trading, but within a digital universe, is exceeding all expectations in testing: over $1.2m of revenue with the first 500 players (out of the 12k+ prelaunch waitlist).
Beyond that major publicly announced partnerships include Warner Music Group, Ubisoft, Dr. Seuss Entertainment and UFC.
We thrilled to be part of the Flow community and are looking forward to seeing the infinite possibilities in truly user-owned content, digital collectibles/accessories as well as applications being realized over the coming years.
For more information on Flow visit onflow.org, Dapper Labs’ medium page and join the discord channel. To start playing NBA Top Shot, visit nbatopshot.com or sign up for beta access here.